Healthcare Storage Virtualization™ (HSV™) specialist grows 40 per cent in 2010 as hospitals in North America and EMEA respond to BridgeHead's unique healthcare data and storage management offerings
Woburn, MA, US and Ashtead, UK - January 11th, 2011 - BridgeHead Software, the Healthcare Storage Virtualization (HSV) company, announced today that its year-over-year income had increased 40 per cent for fiscal year 2010, which ended on September 30. BridgeHead attributed its dynamic 2010 growth to its singular focus on developing and delivering data and storage management offerings that meet the unique needs of the healthcare market.
Just 24 months ago, as the world faced a severe financial crisis, BridgeHead Software underwent a re-organization. Both operations and products were realigned to focus specifically on the healthcare market - a natural strategic evolution given that BridgeHead had already exhibited expertise and a track record of success in this area. This new focus on healthcare has paid off for BridgeHead; the company has grown organically and sustained five consecutive quarters of profitability.
By specializing in healthcare, BridgeHead has been able to capitalize on the US HITECH Act, which provides federal funds for hospital adoption of electronic health records (EHRs), as well as pro-actively developing solutions for the backup and archiving of MEDITECH's health care information system (HCIS) software release. The vertical focus on healthcare has also enabled BridgeHead Software to renew its appeal to NHS trusts in the UK, despite its exclusion from the National Programme for IT (NPfIT) vendors list, and make headway into European public healthcare.
This year, BridgeHead introduced the concept of Healthcare Storage Virtualization (HSV), offering hospitals a new approach to understanding and overcoming some of the difficulties around data and storage management. In essence, HSV enables software applications to be separated from the allocation and management of the physical storage hardware on which the application data resides. This gives healthcare organizations more choice, flexibility and control over the way data is accessed, protected and managed. Ultimately, HSV enables better utilization of existing and future hardware resources and, more importantly, the efficient use of critical electronic patient data. A newly released whitepaper entitled - "Healthcare Storage Virtualization: A New Way of Thinking About Your Data and Storage Management Challenges" is currently available for download.
"Over the course of FY 2010, BridgeHead has reaped the benefits of its reinvention as the Healthcare Storage Virtualization company. In changing our company strategy, we've invested heavily across every division, including the recruitment of new personnel both in our UK and US offices. One of our primary initiatives has been on product development to ensure that we deliver a valuable suite of solutions to hospitals that overcome their specific data and storage management challenges," said BridgeHead founder and CEO Tony Cotterill. "The number of hospitals buying and implementing our technology is a strong validation of BridgeHead's vision: to support the Electronic Health Record and empower healthcare IT to meet their growing storage needs without compromising on current hardware brand or media type."
How BridgeHead Solves Hospital Data and Storage Management Challenges
As it works to solve the data management challenges unique to healthcare organizations, BridgeHead Software has zeroed in on many of the storage pain points that bedevil hospitals all over the world.
Hospitals face a massive upsurge in data growth fueled by the adoption of Electronic Health Records (EHRs) as well as proliferation of DICOM images generated by increasingly prevalent scanning devices. This data tsunami has swamped many hospitals' disaster recovery strategies. As they struggle to manage and control rising healthcare data by purchasing more storage hardware, these same hospitals have also watched their IT budgets ebb away. Because BridgeHead's products and services help hospitals navigate this flood of storage, the company has experienced a rising demand for its healthcare-specific offerings.
Over the past year, BridgeHead has added a significant number of new healthcare customers both in North America and EMEA, expanding its footprint within its existing base. For many of these hospitals, BridgeHead's HSV architecture is providing a long-term roadmap for an effective healthcare disaster recovery (HDR) strategy as well as a blueprint for bringing data management and storage costs under control.
In the United Kingdom, BridgeHead Software has enjoyed increasing levels of interest from the NHS. David Brown, Head of ICT for recent customer The Rotherham NHS Foundation Trust, expressed support for BridgeHead's healthcare-centric approach to storage and data management.
"Clearly for us, and other Trusts, data protection, security, management and storage is absolutely critical to underpin our wider IT initiatives," he explained. "This is why our
relationship with BridgeHead Software has become so important. BridgeHead specializes only in the healthcare market, so they are well placed to understand our data, our hospital environment and our industry; and we're delighted with their progress to date. Over the course of this project, we have been really impressed by the wide range of solutions they offer in backup, disaster recovery and archiving, for both clinical and administrative data. Their knowledge of healthcare makes them a hugely valuable partner - plus, as their products are vendor agnostic, integration with existing systems is not an issue."
BridgeHead Software's largest customer footprint resides in the US where operations run out of Woburn, in the Greater Boston area. As one of BridgeHead's long-standing customers, Mark Middleton, Director of IT Infrastructure at CHRISTUS, commended the company on its expertise regarding data protection from its backup and disaster recovery solutions. "BridgeHead's technology manages all the disk and tape storage media, dynamically allocating volumes and managing the sophisticated archive retention cycles we have set up. This ensures that we are meeting our recovery point and time objectives and data availability commitments in the event of operational failure, disaster, or corruption."
Teaming With Storage Industry Leaders
Over the past 12 months, BridgeHead Software has forged new partnerships with leading storage hardware vendors Dell, Oracle and Iron Mountain while continuing to build on its existing relationships with partners MEDITECH, DB Technology and Perceptive. Dell, Iron Mountain and Oracle have combined their hardware with BridgeHead's software solutions to create comprehensive data and storage management offerings designed specifically for the healthcare industry.
Dell and BridgeHead's joint Medical Archive solution combines the strength of Dell's hardware offerings with the pedigree of BridgeHead's healthcare data management software to create a holistic and fully interoperable enterprise solution for hospitals looking to take control of their digital patient and administrative information. The underlying technology for the joint solution consists of BH MediStore® and BH OfficeStore® from BridgeHead and the DX6000 Object Storage Platform from Dell.
Brett Roscoe, worldwide marketing lead for Dell Enterprise Storage, commented, "We continue to see an exponential growth of storage in healthcare where more and more information is being stored digitally. Organizations require integrated hardware and software solutions that enable them to efficiently store, manage and discover their digital content. Working with Bridgehead Software, we are able to offer customers our storage platform with an industry-leading medical archiving solution from a proven information management leader."
Iron Mountain, the information management company, and BridgeHead's healthcare archiving solution, offers hospitals the opportunity to overcome some of their data management challenges by migrating older content to the Iron Mountain cloud. This significantly relieves the pressure on the hospital's current infrastructure, allowing it to redeploy existing storage assets in a more efficient and effective way (and delaying the need for a storage refresh) while helping with the creation of a "working" and robust backup and disaster recovery strategy - archiving static data into the cloud can reduce the primary backup stream by approximately 80 per cent. And all this with the flexibility, predictability and scalability that comes as part of a cloud solution.
"Hospitals need to have flexibility in their data backup processes to intelligently and cost-effectively handle the needs of the organization for today and in the future," said Ken Rubin, senior vice president and general manager, Healthcare Services for Iron Mountain. "The combined strength of BridgeHead's healthcare data management expertise and Iron Mountain's cloud archiving and disaster recovery capability answers this need. Not only will customers benefit from archiving data to the Iron Mountain cloud with BridgeHead, they can also leverage the solution for offsite backups. Instead of creating backup tapes that must then be removed from a tape library and transported to an offsite location, BridgeHead customers can transfer these backups electronically to redundant, geographically separated databunkers via the Iron Mountain cloud."
BridgeHead Software also worked with Oracle to create HEAT (Healthcare Enterprise Archive Topology), an intelligent archive management architecture that delivers cost effective, long-term data quality and retention for compliance management of healthcare data. Based on an HSV approach, HEAT enables hospitals to combine storage management software from BridgeHead with Oracle's Sun Fire x86 X4270 M2 systems and Oracle's Sun storage and tape systems, including the Sun ZFS Storage Appliance product line and StorageTek SL48 or SL500 Modular Library System to optimize data access and preservation while automating storage management and controlling both capital and operational costs.
Storage and Healthcare Experts Join the Team
To support its focus on the healthcare market, BridgeHead made several strategic additions to its executive leadership team. Michael Ball, PhD, was appointed to the newly created position of senior vice president, North America, and is based at US headquarters in Woburn, MA. Dr. Ball has more than 25 years of marketing and business development experience in the healthcare and IT industries. He comes to BridgeHead from InfoMedics where he was vice president of marketing and professional services for four years.
BridgeHead also appointed two senior executives to new positions in its Ashtead, UK headquarters: Tony Tomkys, director of sales, EMEA, and John McCann, director of marketing.
A seasoned sales professional with over 27 years of experience in IT, Tomkys aims to further increase BridgeHead's UK customer footprint in the NHS and private healthcare sector and will drive pan-European initiatives. He joins BridgeHead Software from CommVault, where he was Business Director for Public Sector. Before that, he held a range of positions from direct sales through to channel management and marketing at companies such as Steria, Morse, HP, Unisys and Apple.
As BridgeHead's director of marketing, John McCann is tasked with overseeing the creation and execution of worldwide marketing strategies that support business growth. With over 15 years experience specializing in B2B IT marketing, McCann came to BridgeHead from Micro Focus where he managed field marketing for the U.K. and Northern Europe. Prior to that, he held positions at software vendors Borland and ADP.
Product Upgrades and Introductions
In addition to rolling out its Healthcare Storage Virtualization architecture, BridgeHead also introduced enhancements and additions to its three core product lines in 2010.
BH MediSafe™ provides the foundation for an effective healthcare disaster recovery (HDR) strategy. By understanding the profile of healthcare data, BridgeHead is able to provide a product set that can more effectively protect healthcare data - not only rapidly changing primary, dynamic data, but also the large volumes of rarely accessed and static tertiary data that hospitals create. A newly released whitepaper entitled - "Healthcare Disaster Recovery: Why Disaster Recovery is Different in Healthcare" is currently available for download.
BH MediStore leverages BridgeHead's underlying and common storage virtualization and data management services to provide a comprehensive solution for managing the clinical and administrative aspects of healthcare data and thereby underpins the electronic health record (EHR). BH MediStore manages and stores: DICOM data for the storage of medical images, scanned documents, and unstructured data files.
A 2010 addition to the MediStore line, BH PACStore®, manages long-term storage and retrieval of PACS imaging data to create a robust, flexible and cost effective enterprise DICOM storage infrastructure. With BH PACStore, healthcare organizations can automatically retain PACS data in a highly protected geographically dispersed fashion and use the most cost effective storage systems dependant on the content's age and value.
BH OfficeStore is a comprehensive solution for the long-term archiving and secure maintenance of all hospital office data, regardless of its original location. By archiving existing content and providing an ideal location for all new user-generated unstructured content, BH OfficeStore relieves the pressure on primary storage and reduces the cost of data ownership.
"In the year to come, BridgeHead Software looks forward to supporting its existing healthcare clients as they move closer towards a full Healthcare Storage Virtualization architecture and implement more of our products," said Cotterill. "At the same time, BridgeHead will be filling out its product offerings both through continued enhancement to our existing products and through the acquisition of products that complement our own."
Healthcare Data Management Thought Leadership
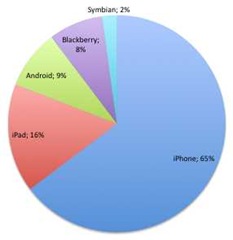
BridgeHead continues to evolve and grow its position as a healthcare data management thought leader. The company published the BridgeHead Software 2010 International Data Management Healthcheck, which measured IT spending by healthcare organizations.
BridgeHead Software, the Healthcare Storage Virtualization (HSV) company, offers a scalable, future-proof platform to overcome rising data volumes and increasing storage
costs while delivering peace of mind around the access, availability and protection of critical electronic patient data. Trusted by more than 1,000 hospitals worldwide, BridgeHead Software solves healthcare organization's backup, recovery and archiving challenges. BridgeHead's HSV solutions are designed to operate with any hospital's chosen software applications and storage hardware, regardless of vendor. This presents healthcare organizations with greater choice, flexibility and control over the manner in which data is accessed, protected and managed. The net effect? Better utilization of hardware resources and, more importantly, the efficient distribution, availability and use of vital healthcare data.
To learn more about BridgeHead Software, visit: http://www.bridgeheadsoftware.com
Follow BridgeHead Software on Twitter at http://www.twitter.com/BridgeHeadHSV
This press release is presented without editing for your information only.
Full Disclosure Statement: The ICT REVIEW received no compensation for any component of this article.